Ruggedized Computer Data Storage 101

Ruggedized storage solutions are critical for defense and industrial applications, giving users the capability to securely store different types of data that is collected during missions and operations. For demanding applications, it is vital that storage solutions are encrypted and expertly ruggedized to ensure that data is not lost or compromised as a result of the adverse and challenging conditions.
Computer storage solutions come in many different shapes and sizes, and can include: hard drives, USB pen/flash drives, CDs, DVDs, and SD cards – to name a few. Whatever its form factor, the underlying reason for storage remains the same: to store input data and allow users to retrieve that data when required.
The storage devices named above are known as ‘non-volatile’, meaning that they will retain the data stored even when power is switched off – they can store important files, media, programs and also your operating system. This storage is different from ‘volatile’ storage, which requires power to retain the stored data, an example of this being RAM (Random Access Memory) and cache memory.
Storage in ruggedized solutions
The hard disk drive (HDD) is a technology that has been around for several decades, and it works by writing data onto a spinning circular disk known as a platter using a moving read/write arm. While the HDD offers a proven, cost-effective solution for storage and is still in widespread use today, it is not an optimum choice for ruggedized computers and servers.
While it is possible to ruggedize HDDs to meet military testing standards such as MIL-STD 810H, which ensures it can survive extreme environmental conditions, the internal moving parts of an HDD – including the platter and arm – struggle to stand up to the extreme shock testing standards that are required under MIL-DTL-901E, not to mention the fact that the data throughput pales in comparison to newer technologies (more on that later in this blog).

For more information on MIL-STD-810H, check out our post: "What is MIL-STD-810H?"
View the Blog PostSolid state drives (SSDs), which have no internal moving parts, have generally replaced HDDs and are widely used across all markets that require ruggedized computer and server solutions. While they are often more expensive than HDDs (though that cost has come down significantly over the past few years), the cost delta is still relatively negligible in a ruggedized solution and is outweighed by the significant amount of performance benefits for the end user that SSDs provide.
For instance, SSDs are very robust and can survive impact forces up to 75 times the force of gravity – or 75G – when expertly ruggedized. They also increase the performance of systems including speeding up the boot up time of operating systems, faster data transfer speeds, and improving system responsiveness when opening and operating a number of applications.
SSDs can utilize what is known as NAND flash memory, which is a non-volatile storage of data and is used across a range of computers, servers and devices for many different applications. There are currently five types of NAND storage, which offer different levels of performance levels at a range of piece points.
The benefits of SSD storage
As well as the durability and performance benefits mentioned above, SSDs also have another key advantage for end users: security.
The SSD can be a self-encrypting device (SED), meaning it can go through the entire encryption and decryption process without any user actions or software – known as transparent encryption – and the data is always protected “at rest” while it is sitting on the storage device, but will behave as a standard SSD when it is unlocked. Encrypting data at rest is clearly of great importance to many customers today, including industrial customers and the military for sensitive and classified files to protect them against malicious cyber actors.
Encryption controllers are generally built directly into the SSD, which means you do not have to burden the CPU with yet more intensive processes such as software encryption, which can see significant performance limitations if you are running a large-array of SSDs. With encryption controllers on the SSD itself, it means that the storage devices can run at their full data transfer speeds.
An encryption standard that many SSDs, and other storage devices, are built to is known as TCG Opal (currently at Version 2.01), a specification set out by the Trusted Computing Group (TCG). If additional security is required, especially if the storage solution will be used in mission-critical government and military applications, then it will also have to meet standards set out by the Federal Information Processing Standard (140-2) – known as FIPS 140-2.
According to the National Institute of Standards and Technology, or NIST, “this standard specifies the security requirements that will be satisfied by a cryptographic module, providing four increasing, qualitative levels intended to cover a wide range of potential applications and environments”. This is more challenging and adds cost, owing to the time and money it takes to qualify a piece of equipment, but the encryption standard is extremely high.
One example of an SSD with government-grade encryption is Seagate’s Nytro products, which can be used in our rackmount server solutions.
How is storage evolving?
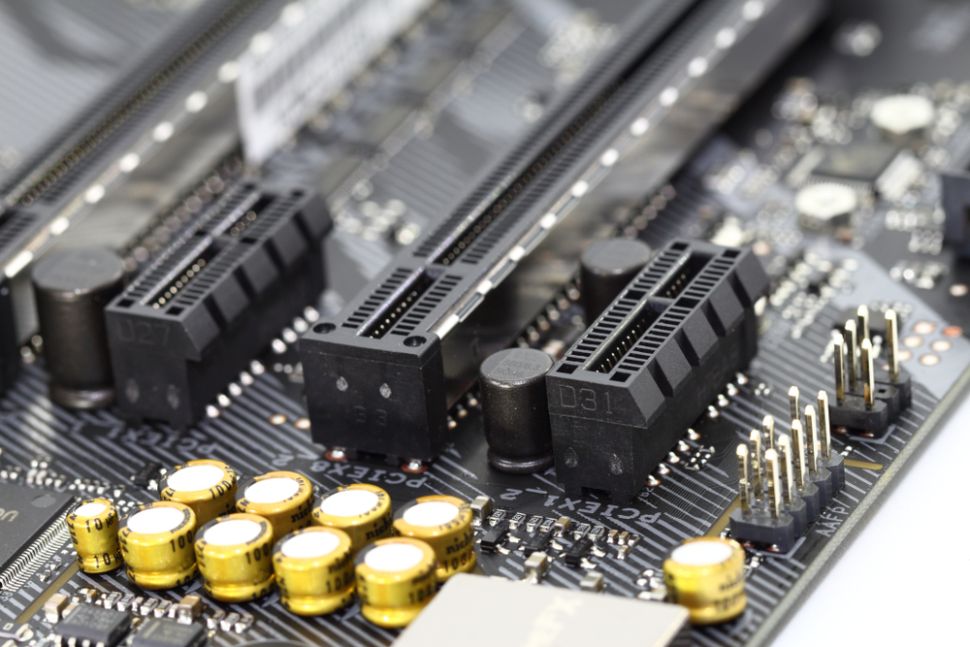
Traditionally, storage devices have interfaced with the motherboard of a computer or server through a Serial ATA (or SATA), with transfer speeds of around 550mb/s. But in recent years, there has been the introduction of high-speed SAS (Serial-Attached SCSI) protocol, which can reach speeds of 2GB/s, and there is now the transition to even faster NVMe for SSDs with speeds of 4GB/s with PCI Gen 3, and 8GB/s with the latest PCI Gen 4.
For more information on PCIe Gen 4, check out our post: "PCIe Gen 4 - Opening the Data Floodgates"
View the Blog PostWith enough drives, it is now possible to reach the speeds of volatile memory such as RAM. This is particularly suited for a number of applications, including building databases for applications such as military signals intelligence (SIGINT) – the collection, processing and analysis of signals across the electromagnetic spectrum – where you have a significant of amount of data being generated and it needs to be stored immediately and retrieved by users rapidly when required.
What is Systel doing?
We provide a range of data storage options in our rackmount server and embedded computer product categories, meeting requirements for defense and commercial applications. Our compute solutions are purpose-built to meet exacting specifications including data storage throughput, capacity, and security requirements.
Let's Talk!
Have questions or want to learn more?
Contact our team and let’s talk!